Case study
This assignment will be based on the following news article:
Ragan, S 2017 ‘Office 365 Phishing attacks create a sustained insider nightmare for IT’, CSO Online, 20 September, <https://www.csoonline.com/article/3225469/office-365-phishing-attacks-create-a-sustained-insider-nightmare-for-it.html>
Answer the following questions in relation to the news article. Assume that the audience for your responses is senior level management, who do not have a strong technical background. The word limit for this assessment item is 900 words.
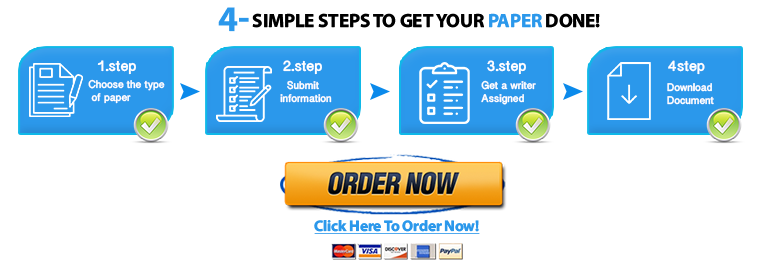
Save your time - order a paper!
Get your paper written from scratch within the tight deadline. Our service is a reliable solution to all your troubles. Place an order on any task and we will take care of it. You won’t have to worry about the quality and deadlines
Order Paper Now1. Characterise the social engineering attacks described in the article using the ontological components specified in Mouton et al (2016) as a starting point.
2. Discuss relevant statistics (for example, from the Verizon Data Breach Investigations Report) in relation to these types of attacks.
3. Outline the typical sequence of steps undertaken for the phishing attacks described in the article.
4. Propose and justify potential mitigations for these types of attacks. Include consideration of people, process and technology factors.
Mouton, F, Leenen, L and Venter, H S 2016, ‘Social engineering attack examples, templates and scenarios’, Computers & Security, vol. 59, pp.186-209.
"Looking for a Similar Assignment? Order now and Get 10% Discount! Use Code "Newclient"