Computer security foundations
· Recognizing the importance of security policies
· Understanding the various policies and the rationale for them.
· Knowing what elements go into good policies
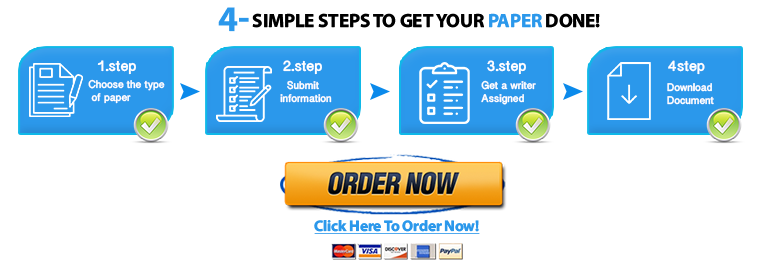
Save your time - order a paper!
Get your paper written from scratch within the tight deadline. Our service is a reliable solution to all your troubles. Place an order on any task and we will take care of it. You won’t have to worry about the quality and deadlines
Order Paper Now· Creating policies for network administration.
Using the guidelines provided in this week’s chapter (and other resources as needed), create a step-by-step IT security policy for handling user accounts/rights for a student who is leaving prematurely (drops, is expelled, and so on).
You will need to consider specialized student scenarios, such as a student who works as an assistant to a faculty member or as a lab assistant in a computer lab and may have access to resources most students do not.
Write your answer using a WORD document. Do your own work. Note your Safe Assign score. Score must be less than 25 for full credit.
"Looking for a Similar Assignment? Order now and Get 10% Discount! Use Code "Newclient"